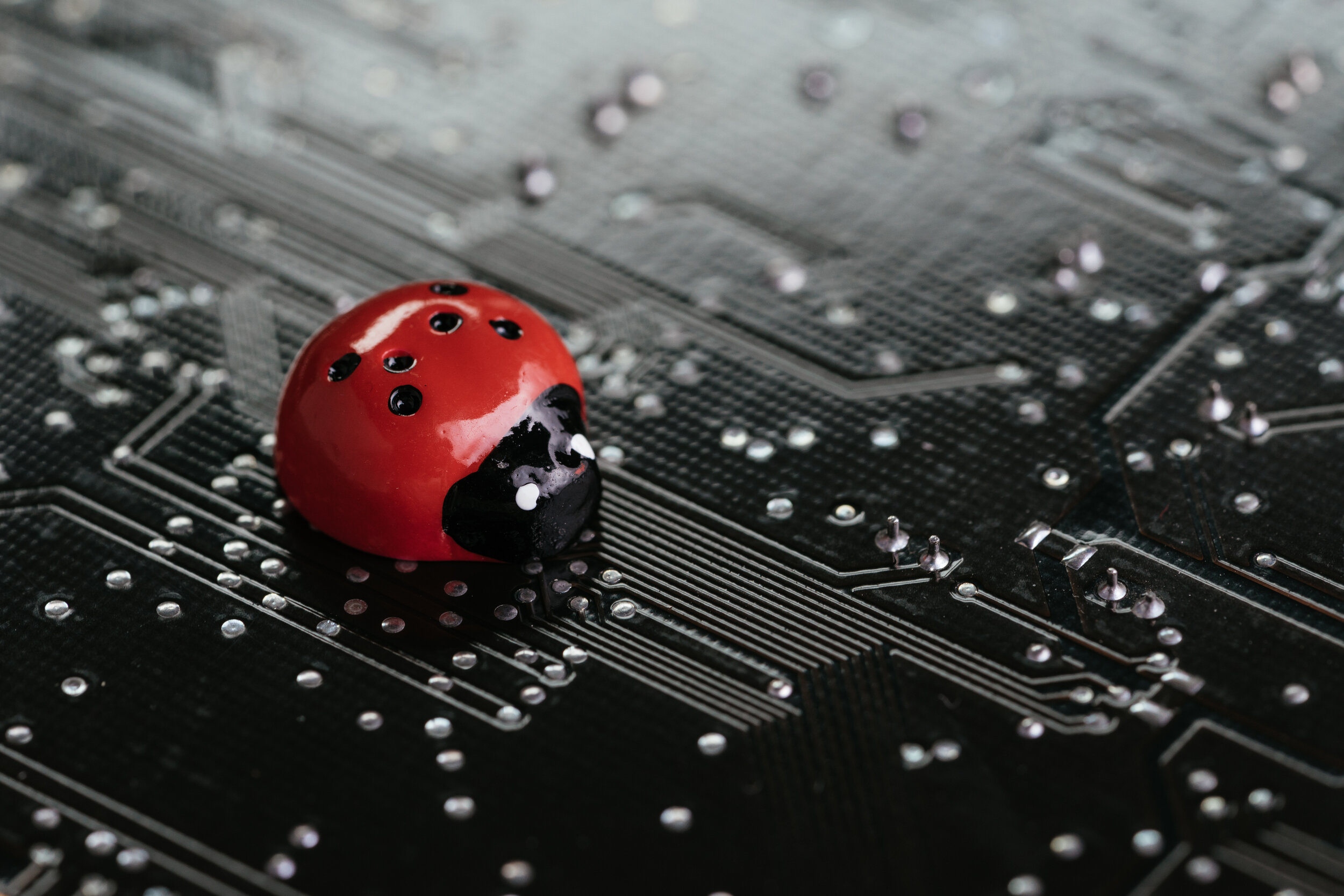
It's almost always a bad idea to write more than a few lines of code, assume they work as intended, and move on to a separate task. Even after the change compiles successfully, and even after code reviews, there's always the chance that some underlying assumption turns out to be wrong, yielding unexpected results in edge cases. Once such a bug is introduced, it might linger for long periods of time if that section of code isn't in frequent use.
Read MoreIn the infancy of computing, passwords relied heavily on trust. These early passwords were relatively short and simple. As the trust eroded and the threat model changed, we started to enforce restrictions around passwords such as minimum length and using encrypted passwords for system access. As computing continued to evolve, it became even easier to guess or manipulate passwords thereby driving more artificial complexity and, ultimately, user hate and non-compliance.
Let’s take a step back, evaluate some password threats, review their protections, and challenge evolving complexity requirements.
Read MoreThere is no silver bullet to security, and even more importantly, there is no single source of truth for what security options are available, what they do, and what impacts they have, or even how they all work together.
In this post, we will enumerate the many security mechanisms that can be operationally deployed in an embedded system running Linux in order to secure that system from common software attacks. While the traditional approach to security relies on the CIA triad of confidentiality, integrity, and availability, the majority of this post is primarily focused on the principles and enforcement of integrity.
Read MoreIt's not fair.
When attacking an embedded system, it takes only one vulnerability to lead to an exploit.
This means, when tasked with securing an embedded system, the defender must think through and be prepared to protect against every possible vulnerability. Overlook just one opening and the attacker may find it, take control, steal your secrets, and create an exploit for others to use anytime, anywhere.
Worse yet, that same attacker may use an initial compromised device to pivot from one exploited subsystem to another, causing further damage to your network, mission, and reputation.
In this blog post, we present the Top 10 properties of highly-secure embedded systems – insight that is based upon decades of experience engineering security solutions across a number of high-value military and commercial platforms.
Read MoreWhile we don’t yet know all the details, the recent SolarWinds Orion compromise brings to light a key tenant of software distribution and secure systems; namely that signing software release packages in a secure fashion is absolutely paramount. But it also helps us realize there is no magic bullet for security, and defense-in-depth must be realized at all levels of the software development lifecycle.
Read MoreDon’t get upset.
We fully acknowledge that the hard-working people who make enterprise type Linux distributions want to help their customers achieve secure systems and they strive to improve the security posture of their distributions all the time.
However, there are two major areas where these developers run up against a nearly insurmountable wall.
First, they use a different threat model. An enterprise distribution of Linux is designed with a threat model suited to datacenter/cloud deployments, but embedded and cyber-physical systems face a wider array of threats including situations where the attacker may have physical access to the system.
Second…
Read MoreIn September of 2020, a team at the Systems and Network Security Group at VU Amsterdam announced a new technique for developing exploits they called BlindSide [1].
BlindSide allows an attacker to conduct Blind ROP-style [2] attacks against targets that are not crash-resistant, such as the Linux kernel. What does this mean for you as a system engineer? It means BlindSide can enable an attacker with knowledge of a single kernel overflow vulnerability to convert an unprivileged shell to a root shell despite recent kernel features designed to prevent information leaks which can lead to these types of privilege escalations.
It is techniques like BlindSide, and other techniques still unknown, that drive Star Lab to design its products with the assumption that an attacker will gain root access. It is why we advocate everyone at least consider…
Read MoreOn August 13th, 2020, The National Security Agency and Federal Bureau of Investigations released a cybersecurity advisory that warned anyone deploying or maintaining a Linux system about a new Russian (and now worldwide) cyber espionage threat named Drovorub. Of course, this isn't the first time a government-sponsored cyber threat has found its way into the wild. But its newsworthiness lies not in its origin, novelty, or effectiveness, but in the fact that it can be completely prevented to begin with.
Read MoreProtecting endpoints is hard. Understatement of the millennium, right?
Protecting unmanaged endpoints is even harder. Doubtful that surprises anyone.
Protecting mission-critical, unmanaged endpoints? Well, saying it's impossible is a stretch, but superlatives are warranted.
One of the most common goals in system security is maintaining system integrity. Knowing what is running (or can run) on the deployed system is critical, especially in embedded and unmanaged use cases.
Enterprise and managed endpoints are not immune from these concerns either.
The countless servers and devices that drive the modern world and economy require the same assurances; the difference being the enterprise world usually has more infrastructure and connectivity to achieve these goals.
If we roll back the clocks to early 2018, maintaining system integrity was already a…
Read MoreCybersecurity is the persistent, multi-disciplined practice required to ensure confidence and trust in complex information systems.
Humans depend upon operational technology (OT) systems for their livelihood, safety, and security. Maintaining the chain of security is fundamental across every stage of system design, engineering, configuration, operation, maintenance, and disposition.
A single weak link has the potential to break the security chain. In order to prevent weak links and provide high levels of assurance, secure design principles and security best practices must be applied throughout the system lifecycle – from requirements definition through operations and maintenance.
Read More